As much as I hate that website more than anything else on the Internet, I've made an account. Mainly for the same reasons I use AOL for instant messaging: all my friends use it.
Actually it was my niece's friend who set up my account.
If you can't find it, I probably don't want you reading it.
Thursday, July 31, 2008
Monday, July 21, 2008
My Computer Sucks
It looks like yet another one of my computer components is dying. So I feel like going on a rant...
My monitor turns itself off a second after I turn it on, then it comes on again for a second and turns off again. It does this for about 5 minutes after I turn it on.
My motherboard's fan quit spinning as fast, causing my chipset to overheat and all but 3 (thank God) of my USB ports don't work anymore. I even bought an extended warranty for it because I have so much bad luck with computer parts, but of course, this happened shortly after the warranty expired.
My video card's memory heatsinks fell off and I had to special order heatsink glue to reattach them. Also it mysteriously runs at 85 celcius under load. (Yes, I've cleaned the dust off of it and I have 12cm intake and exhaust fans.)
My processor turned out to be defective too. Fortunately it was under warranty.
My old laptop's video card died twice due to a manufacturing defect. The hard drive also died.
My new laptop's motherboard died a month after I bought it. Actually I bought it used, and this occured 3 months after the warranty expired (of course).
My iPod's hard drive died 2 years after I bought it.
All right, hopefully this wasn't too depressing. Enjoy the rest of my blog! :)
My monitor turns itself off a second after I turn it on, then it comes on again for a second and turns off again. It does this for about 5 minutes after I turn it on.
My motherboard's fan quit spinning as fast, causing my chipset to overheat and all but 3 (thank God) of my USB ports don't work anymore. I even bought an extended warranty for it because I have so much bad luck with computer parts, but of course, this happened shortly after the warranty expired.
My video card's memory heatsinks fell off and I had to special order heatsink glue to reattach them. Also it mysteriously runs at 85 celcius under load. (Yes, I've cleaned the dust off of it and I have 12cm intake and exhaust fans.)
My processor turned out to be defective too. Fortunately it was under warranty.
My old laptop's video card died twice due to a manufacturing defect. The hard drive also died.
My new laptop's motherboard died a month after I bought it. Actually I bought it used, and this occured 3 months after the warranty expired (of course).
My iPod's hard drive died 2 years after I bought it.
All right, hopefully this wasn't too depressing. Enjoy the rest of my blog! :)
Thursday, July 17, 2008
Anonymous P2P
As someone who is pursuing a graduate degree in computer networks and someone who wants to be a network security expert (and, if you've read the rest of my posts, someone who's on the MPAA's watch list), I've been digging into anonymous file sharing networks. I've known for a long time (almost as long as I've been using the Internet) that online activities are very susceptible to eavesdropping, monitoring, data mining, and flagrant breaches of privacy.
File sharing networks have come under the most fire lately by the powers that be. Regardless of your opinions about them, securing them remains challenging. Several people have already taken a crack at this problem, and though none have really solved it in a way that is fit for mainstream users, I wanted to examine some of their work. No implementation is perfect, but I have discovered that some are definitely better than others.
First, let's start with Tor. If you want to be able to browse the web anonymously, without being eavesdropped, it's the best way to go. It doesn't require you to upload any traffic, and it provides SOCKS5 functionality, so it works with almost any TCP application. Also, at 117.5kbps, Tor wins the download speed contest for web traffic.
What Tor does not do very well is handle large amounts of data, which makes it a poor choice for file sharing applications. Additionally, Tor cycles between exit nodes rapidly, causing your public IP address to change, which file sharing software also does not like.
I2P was designed more with file sharing in mind, though you wouldn't know it if you just downloaded their Java-based router application. It takes a bit more thinking to figure out how to use I2P than Tor, but I2P seems to be a good alternative to Tor.
Firing up I2P's router console reveals several ways to use the network. There's an http proxy, IRC, POP3/SMTP, and a few other protocols. The whole thing is very community-based: when you open up I2P, you feel like you're a part of a whole secret Internet society. It's like a club, and you'll feel like you were logging on to the Internet for the first time back in the 1990s.
Unfortunately, just like the old Internet, I2P's connection is a high-latency, low-bandwidth one. Also, I2P's main difference from Tor is that it doesn't offer a SOCKS proxy. Instead, it requires all applications used on it to be specifically written for it. It does come with a lightweight BitTorrent client, but getting eDonkey to work was a real PITA. And at 29kbps for web downloads, I2P's web proxy is slow.
Some developers have created iMule: a special mod of the aMule eDonkey client for the I2P network. I first tried unzipping it to a folder and running imule.exe, per the instructions. After a while, it successfully connected to the I2P network, but it would not connect to Kademlia (it does not support eDonkey servers). I figured out the nodes.dat file it was trying to download was giving me a 404 error, so I scoured the Internet for a fresh list and input it into iMule. A few seconds later, iMule crashed.
I was able to get help on I2P's IRC channels, but never ended up fixing the problem. But I did discover something disappointing about iMule and their BitTorrent client: they only connect to other peers that are on I2P.
AntsP2P was the next thing I tried. It is an anonymous file sharing network, not an overlay or proxy network like Tor and I2P. Since it has been designed explicitly for file sharing, I expected its performance to be pretty good. (With iMule and I2P BitTorrent not working, neither of the two previous networks I tested support P2P programs.)
With only an average of 10 peers, AntsP2P is just about dead. There were no files when I searched for anything. Not even the letter 'a'.
MUTE was the next thing I tried. I searched for the letter 'a' and it actually returned results! I downloaded one of the files, at about 10KB/s. The client said it was corrupted, I was able to open it just fine (it was a PDF). Still, when a client reports corruption but doesn't do anything to fix it, you know the development team has a lot of work to do.
Well, of all the clients I tested, only Tor and MUTE ended up working at all. Tor works reasonably well but shouldn't be used for file sharing. MUTE is slow and prone to corruption, so I just can't recommend it. Plus its selection of files is very limited. For now, if you want to get into file sharing, you'll still have to deal with the AAs.
File sharing networks have come under the most fire lately by the powers that be. Regardless of your opinions about them, securing them remains challenging. Several people have already taken a crack at this problem, and though none have really solved it in a way that is fit for mainstream users, I wanted to examine some of their work. No implementation is perfect, but I have discovered that some are definitely better than others.
First, let's start with Tor. If you want to be able to browse the web anonymously, without being eavesdropped, it's the best way to go. It doesn't require you to upload any traffic, and it provides SOCKS5 functionality, so it works with almost any TCP application. Also, at 117.5kbps, Tor wins the download speed contest for web traffic.
What Tor does not do very well is handle large amounts of data, which makes it a poor choice for file sharing applications. Additionally, Tor cycles between exit nodes rapidly, causing your public IP address to change, which file sharing software also does not like.
I2P was designed more with file sharing in mind, though you wouldn't know it if you just downloaded their Java-based router application. It takes a bit more thinking to figure out how to use I2P than Tor, but I2P seems to be a good alternative to Tor.
Firing up I2P's router console reveals several ways to use the network. There's an http proxy, IRC, POP3/SMTP, and a few other protocols. The whole thing is very community-based: when you open up I2P, you feel like you're a part of a whole secret Internet society. It's like a club, and you'll feel like you were logging on to the Internet for the first time back in the 1990s.
Unfortunately, just like the old Internet, I2P's connection is a high-latency, low-bandwidth one. Also, I2P's main difference from Tor is that it doesn't offer a SOCKS proxy. Instead, it requires all applications used on it to be specifically written for it. It does come with a lightweight BitTorrent client, but getting eDonkey to work was a real PITA. And at 29kbps for web downloads, I2P's web proxy is slow.
Some developers have created iMule: a special mod of the aMule eDonkey client for the I2P network. I first tried unzipping it to a folder and running imule.exe, per the instructions. After a while, it successfully connected to the I2P network, but it would not connect to Kademlia (it does not support eDonkey servers). I figured out the nodes.dat file it was trying to download was giving me a 404 error, so I scoured the Internet for a fresh list and input it into iMule. A few seconds later, iMule crashed.
I was able to get help on I2P's IRC channels, but never ended up fixing the problem. But I did discover something disappointing about iMule and their BitTorrent client: they only connect to other peers that are on I2P.
AntsP2P was the next thing I tried. It is an anonymous file sharing network, not an overlay or proxy network like Tor and I2P. Since it has been designed explicitly for file sharing, I expected its performance to be pretty good. (With iMule and I2P BitTorrent not working, neither of the two previous networks I tested support P2P programs.)
With only an average of 10 peers, AntsP2P is just about dead. There were no files when I searched for anything. Not even the letter 'a'.
MUTE was the next thing I tried. I searched for the letter 'a' and it actually returned results! I downloaded one of the files, at about 10KB/s. The client said it was corrupted, I was able to open it just fine (it was a PDF). Still, when a client reports corruption but doesn't do anything to fix it, you know the development team has a lot of work to do.
Well, of all the clients I tested, only Tor and MUTE ended up working at all. Tor works reasonably well but shouldn't be used for file sharing. MUTE is slow and prone to corruption, so I just can't recommend it. Plus its selection of files is very limited. For now, if you want to get into file sharing, you'll still have to deal with the AAs.
Saturday, July 12, 2008
I Can't Drive 55
It looks like the government is looking at bringing back the 55 MPH speed limit to try and bring down the price of gas.
Didn't they learn their lesson when they tried this before? It didn't work for the same reason prohibition didn't work: nobody did it. I know if they reinstate it, I sure won't. Instead, I'll be buying products (and stock, if they decide to go IPO) from this company.
Besides, wouldn't they conserve even more energy if they lowered the speed limit to 45? Or prohibited the use of air conditioning? I would think high gas prices are exactly what environmentalists would want.
Didn't they learn their lesson when they tried this before? It didn't work for the same reason prohibition didn't work: nobody did it. I know if they reinstate it, I sure won't. Instead, I'll be buying products (and stock, if they decide to go IPO) from this company.
Besides, wouldn't they conserve even more energy if they lowered the speed limit to 45? Or prohibited the use of air conditioning? I would think high gas prices are exactly what environmentalists would want.
Thursday, July 10, 2008
Wanted
I finally got my first complaint from the MPAA! Here it is, in its full glory!
Dear Subscriber:
This email is being sent to you by Road Runner Customer Care because we have received a complaint that your computer has been used to distribute copyrighted material without authorization through a peer-to-peer program. We received this complaint from the movie studio, record company, television studio or other company that owns the copyrighted material. The purpose of this email is to remind you that the distribution of copyrighted material in this fashion may violate both the copyright laws and Road Runner's terms of service, and to tell you a bit about peer-to-peer programs, the dangers they can pose to your computer and our network, and the steps you can take to protect yourself.
A computer can become accessible to a peer-to-peer network for an unlimited period of time after a peer-to-peer program is downloaded.
You may not even be aware that such a program is on your computer; a child or a visitor to the home could have downloaded it. That is why we want to alert you to this issue. Peer-to-peer programs may contain many problems. For example:
· Downloading and offering for upload copyrighted material without authorization is unlawful. If you or others using your computer have been doing this, you could be subject to civil penalties and criminal fines. Such activity also violates the Road Runner terms of service.
· The programs allow any anonymous person on the Internet to look at your computer files and copy them for themselves. Such a hacker could view all of your files, which can lead to identity theft.
· The programs, which use large amounts of memory, can interfere with the functioning of your computer by destabilizing your operating system, leading to a general sluggishness at bootup and during operation.
· The programs can contain spyware, adware, malware, viruses and pornography.
If you are interested in a discussion of problems associated with peer-to-peer file sharing, please follow this link: http://research.pestpatrol.com/whitepapers/p2p_impact.asp.
If you use the Windows OS, the best way to remove peer-to-peer programs is through the Add/Remove Programs tool. Other removal options are discussed at http://security.uchicago.edu/peer-to-peer/no_fileshare.shtml.
Thank you for subscribing to Road Runner.
Very truly yours,
Road Runner Customer Care
Original Message Follows:
------------------------
ISP: Time Warner Cable
IP Address: [censored]
Tuesday, April 29, 2008
Re: Unauthorized Copying and Distribution of Copyrighted Audiovisual Works
Dear Sir/Madam:
I am contacting you on behalf of the Motion Picture Association of America ("MPAA") and one or more of its member companies.
We submit that the MPAA is authorized to act on behalf of its member companies (the "MPAA Members") with respect to the matter described in this notice. The MPAA Members own intellectual property rights, including exclusive rights protected under copyright law, in many motion pictures, television programs and other audiovisual works (collectively, the "MPAA Titles"). We believe that your Time Warner Cable Internet account is being used to reproduce and/or distribute copies of one or more MPAA Titles on the Internet, in violation of the MPAA Members' legal rights. We have set forth at the close of this letter the details concerning this infringement, including the title(s) of the MPAA Title(s) in question, the IP address of your account at the time of the infringement, and the date and time of the infringement. The audiovisual works being offered through your Internet account include the following:
Office, The (TV)
The copying and/or distribution of copies of copyrighted audiovisual works without the authorization of the copyright owner constitutes copyright infringement under the U.S. Copyright Act, 17 U.S.C. §§ 106, 501. This conduct may subject you to significant liability, including statutory damages of up to $150,000 per infringed work for willful infringement. Under certain circumstances, copyright infringement can give rise to federal criminal liability, with penalties as high as five years imprisonment plus a $250,000 fine. (See 17 U.S.C. § 506; 18 U.S.C. § 2319.)
Such infringing activity also constitutes a violation of Time Warner Cable's Abuse Policy/Terms of Service Agreement, and such breach may give Time Warner Cable the right to terminate your Internet access service. We therefore demand that you immediately:
1) Cease any unauthorized offering or downloading of the above title(s), and any other film or television titles whose copyright is owned by the MPAA Members, on any peer-to-peer or other internet services; and 2) Delete from your computer any unauthorized copies of the above title(s), and any other film or television titles owned by the MPAA Members, which you have downloaded from or offered on any peer-to-peer or other internet services.
You can learn more about piracy by visiting the MPAA's web site at http://www.mpaa.org/piracy.asp. If you have any questions about this notice, you may contact us at:
Telephone: 818-475-1727
Email: notices@motionpictureassociation.org
Motion Picture Association of America, Inc.
15301 Ventura Blvd., Building E
Sherman Oaks, CA 91403
United States
Please include the Case ID 485049453 in the subject line of any correspondence.
This letter is not a complete statement of the Copyright Owners' rights in connection with this matter, and nothing contained herein constitutes an express or implied waiver of any rights, remedies or defenses of the Copyright Owners, all of which are expressly reserved.
Very truly yours,
Motion Picture Association of America
------------------------------
INFRINGEMENT DETAIL
--------------------
Infringing Work: Office, The (TV)
First Found: 21 Apr 2008 14:22:57 EDT (GMT -0400)
Last Found: 21 Apr 2008 14:22:57 EDT (GMT -0400)
IP Address: [censored]
IP Port: 6886
Protocol: BitTorrent
Torrent InfoHash: 459A6F0D7C39517FC9E31DC29A8551970E720A16
Containing file(s):
The.Office.US.S04E10.HDTV.XviD-LOL.[VTV].avi (183,535,616 bytes)
Dear Subscriber:
This email is being sent to you by Road Runner Customer Care because we have received a complaint that your computer has been used to distribute copyrighted material without authorization through a peer-to-peer program. We received this complaint from the movie studio, record company, television studio or other company that owns the copyrighted material. The purpose of this email is to remind you that the distribution of copyrighted material in this fashion may violate both the copyright laws and Road Runner's terms of service, and to tell you a bit about peer-to-peer programs, the dangers they can pose to your computer and our network, and the steps you can take to protect yourself.
A computer can become accessible to a peer-to-peer network for an unlimited period of time after a peer-to-peer program is downloaded.
You may not even be aware that such a program is on your computer; a child or a visitor to the home could have downloaded it. That is why we want to alert you to this issue. Peer-to-peer programs may contain many problems. For example:
· Downloading and offering for upload copyrighted material without authorization is unlawful. If you or others using your computer have been doing this, you could be subject to civil penalties and criminal fines. Such activity also violates the Road Runner terms of service.
· The programs allow any anonymous person on the Internet to look at your computer files and copy them for themselves. Such a hacker could view all of your files, which can lead to identity theft.
· The programs, which use large amounts of memory, can interfere with the functioning of your computer by destabilizing your operating system, leading to a general sluggishness at bootup and during operation.
· The programs can contain spyware, adware, malware, viruses and pornography.
If you are interested in a discussion of problems associated with peer-to-peer file sharing, please follow this link: http://research.pestpatrol.
If you use the Windows OS, the best way to remove peer-to-peer programs is through the Add/Remove Programs tool. Other removal options are discussed at http://security.uchicago.edu/
Thank you for subscribing to Road Runner.
Very truly yours,
Road Runner Customer Care
Original Message Follows:
------------------------
ISP: Time Warner Cable
IP Address: [censored]
Tuesday, April 29, 2008
Re: Unauthorized Copying and Distribution of Copyrighted Audiovisual Works
Dear Sir/Madam:
I am contacting you on behalf of the Motion Picture Association of America ("MPAA") and one or more of its member companies.
We submit that the MPAA is authorized to act on behalf of its member companies (the "MPAA Members") with respect to the matter described in this notice. The MPAA Members own intellectual property rights, including exclusive rights protected under copyright law, in many motion pictures, television programs and other audiovisual works (collectively, the "MPAA Titles"). We believe that your Time Warner Cable Internet account is being used to reproduce and/or distribute copies of one or more MPAA Titles on the Internet, in violation of the MPAA Members' legal rights. We have set forth at the close of this letter the details concerning this infringement, including the title(s) of the MPAA Title(s) in question, the IP address of your account at the time of the infringement, and the date and time of the infringement. The audiovisual works being offered through your Internet account include the following:
Office, The (TV)
The copying and/or distribution of copies of copyrighted audiovisual works without the authorization of the copyright owner constitutes copyright infringement under the U.S. Copyright Act, 17 U.S.C. §§ 106, 501. This conduct may subject you to significant liability, including statutory damages of up to $150,000 per infringed work for willful infringement. Under certain circumstances, copyright infringement can give rise to federal criminal liability, with penalties as high as five years imprisonment plus a $250,000 fine. (See 17 U.S.C. § 506; 18 U.S.C. § 2319.)
Such infringing activity also constitutes a violation of Time Warner Cable's Abuse Policy/Terms of Service Agreement, and such breach may give Time Warner Cable the right to terminate your Internet access service. We therefore demand that you immediately:
1) Cease any unauthorized offering or downloading of the above title(s), and any other film or television titles whose copyright is owned by the MPAA Members, on any peer-to-peer or other internet services; and 2) Delete from your computer any unauthorized copies of the above title(s), and any other film or television titles owned by the MPAA Members, which you have downloaded from or offered on any peer-to-peer or other internet services.
You can learn more about piracy by visiting the MPAA's web site at http://www.mpaa.org/piracy.
Telephone: 818-475-1727
Email: notices@
Motion Picture Association of America, Inc.
15301 Ventura Blvd., Building E
Sherman Oaks, CA 91403
United States
Please include the Case ID 485049453 in the subject line of any correspondence.
This letter is not a complete statement of the Copyright Owners' rights in connection with this matter, and nothing contained herein constitutes an express or implied waiver of any rights, remedies or defenses of the Copyright Owners, all of which are expressly reserved.
Very truly yours,
Motion Picture Association of America
------------------------------
INFRINGEMENT DETAIL
--------------------
Infringing Work: Office, The (TV)
First Found: 21 Apr 2008 14:22:57 EDT (GMT -0400)
Last Found: 21 Apr 2008 14:22:57 EDT (GMT -0400)
IP Address: [censored]
IP Port: 6886
Protocol: BitTorrent
Torrent InfoHash: 459A6F0D7C39517FC9E31DC29A8551
Containing file(s):
The.Office.US.S04E10.HDTV.
Sunday, July 6, 2008
My grammar is fine!
All you dumbasses who wrote to me to tell me that the title of my blog should be Chris' Two Cents are wrong!
Smiles, giggles, and cinnamon!
Smiles, giggles, and cinnamon!
Thursday, July 3, 2008
Business
As I mentioned in my previous post, I'm trying to get into the business of providing computer support. At first, my plan is to start doing what I have the most experience with: solving Windows problems for home and business users.
Well, there are a lot of people out there making a living doing just that, but I have the knowledge to do much more, just not the experience. For example, one of my recent hobbies has been learning to use Linux. Now that I've crossed that hurdle, I need to figure out how to fix and maintain it so I can make some money.
Learning how to use a new operating system, for me at least, isn't a time-consuming or very difficult affair, but learning how to dig into its guts is. I'm a very intuitive person, but to learn how to repair Linux requires a lot of reading, which takes time.
Besides Linux, I also have this fancy $100,000 college degree in computer science that I'm not doing anything with. Computer Science is the study of how computer programs are created and how they operate. So it's really the next level of knowledge. I've discovered these levels of knowledge can be applied to all kinds of products. In ascending order of specialty, there are three types of people: those who know how to use a product, those who know how to fix it, and those who know how to make it. (Well, I guess there's a fourth: those who don't know anything.)
I'll continue this philosophical discussion in a future post. For now, I want to talk about two different business models that I'm testing.
The first is the one I started trying last September. It's a little more traditional, but still is 100% Internet based. What I did is I created a computer repair web site that looks just like a business. It has a business name, its own phone number, prices, hours, and everything else you'd expect. I placed ads on yellowpages.com, Yahoo's directory, and a couple others. Currently I'm spending $60 each month on advertising and I'm getting almost no business. Usually not even enough to cover my advertising costs.
The second business model that I'm experimenting with takes a more candid approach. Instead of a me-dot-com web site, I'm using the space my alma mater gave me. On it, I have a support page that tells everyone I'm a college student looking to make a few bucks that will do the same jobs Geek Squad will for a lot less. It tells everyone I have a degree in computer science and I know what I'm doing. The .edu domain validates my status as a student, and also gives my PageRank a boost, hopefully along with my credibility.
Speaking of credibility, my student web site needs it. My commercial web site just looks a whole lot better. For one thing, it has a name, and my student page doesn't. But it's also laiden with tables and old web site design principles. So I need to spend some time learning the newer techniques and brush it up.
I also need to get people to view the web site. Google has sent me an email offering me $50 in free advertising. At first, I thought the ads would cost $0.10 per click like they did in the 90s, but I soon discovered that some keywords can cost as much as $10 per click!
So I've been reading a few things about how AdSense and AdWords work. Hopefully, I'll be able to pool all this information together and not only get cheap advertising, but also make some money by putting ads up on my own web site.
For now, I've got work to do. If you need something else to read, read my web site!
Well, there are a lot of people out there making a living doing just that, but I have the knowledge to do much more, just not the experience. For example, one of my recent hobbies has been learning to use Linux. Now that I've crossed that hurdle, I need to figure out how to fix and maintain it so I can make some money.
Learning how to use a new operating system, for me at least, isn't a time-consuming or very difficult affair, but learning how to dig into its guts is. I'm a very intuitive person, but to learn how to repair Linux requires a lot of reading, which takes time.
Besides Linux, I also have this fancy $100,000 college degree in computer science that I'm not doing anything with. Computer Science is the study of how computer programs are created and how they operate. So it's really the next level of knowledge. I've discovered these levels of knowledge can be applied to all kinds of products. In ascending order of specialty, there are three types of people: those who know how to use a product, those who know how to fix it, and those who know how to make it. (Well, I guess there's a fourth: those who don't know anything.)
I'll continue this philosophical discussion in a future post. For now, I want to talk about two different business models that I'm testing.
The first is the one I started trying last September. It's a little more traditional, but still is 100% Internet based. What I did is I created a computer repair web site that looks just like a business. It has a business name, its own phone number, prices, hours, and everything else you'd expect. I placed ads on yellowpages.com, Yahoo's directory, and a couple others. Currently I'm spending $60 each month on advertising and I'm getting almost no business. Usually not even enough to cover my advertising costs.
The second business model that I'm experimenting with takes a more candid approach. Instead of a me-dot-com web site, I'm using the space my alma mater gave me. On it, I have a support page that tells everyone I'm a college student looking to make a few bucks that will do the same jobs Geek Squad will for a lot less. It tells everyone I have a degree in computer science and I know what I'm doing. The .edu domain validates my status as a student, and also gives my PageRank a boost, hopefully along with my credibility.
Speaking of credibility, my student web site needs it. My commercial web site just looks a whole lot better. For one thing, it has a name, and my student page doesn't. But it's also laiden with tables and old web site design principles. So I need to spend some time learning the newer techniques and brush it up.
I also need to get people to view the web site. Google has sent me an email offering me $50 in free advertising. At first, I thought the ads would cost $0.10 per click like they did in the 90s, but I soon discovered that some keywords can cost as much as $10 per click!
So I've been reading a few things about how AdSense and AdWords work. Hopefully, I'll be able to pool all this information together and not only get cheap advertising, but also make some money by putting ads up on my own web site.
For now, I've got work to do. If you need something else to read, read my web site!
First Post!
Hi there. My name is Chris and I created this blog mainly to document my activities that myself and others might find remotely useful, funny, or interesting.
I'm currently going to UCI full time to get a master's degree in networked systems (computer science). I also have a real web site with computer guides and some of my school work.
Most importantly, I am trying to go into business for myself while I'm in school, doing computer work. If you're interested, here's some more information.
I'm currently going to UCI full time to get a master's degree in networked systems (computer science). I also have a real web site with computer guides and some of my school work.
Most importantly, I am trying to go into business for myself while I'm in school, doing computer work. If you're interested, here's some more information.
Subscribe to:
Posts (Atom)
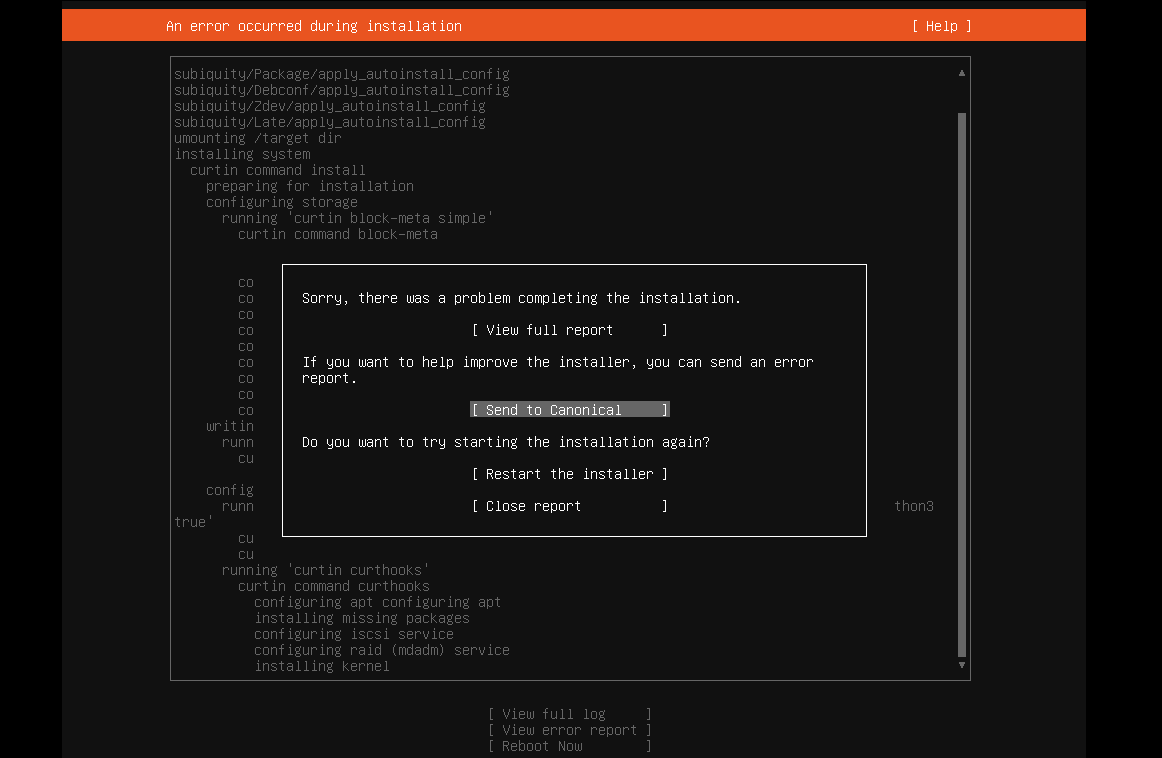
Ubuntu 22.04 on VMware Workstation Error
I tried installing Ubuntu 22.04 server on VMware Workstation and got this message: Sorry, there was a problem completing the installation E...
-
We have a customer at work that runs Dentrix. They have 4 offices, and need to have all of the patient data in one place. Unfortunately,...
-
I tried installing Ubuntu 22.04 server on VMware Workstation and got this message: Sorry, there was a problem completing the installation E...
-
I was having a problem with audio latency in VMware Workstation on my Windows 10 guest. I found an article that helped me fix it. Ever sin...
